«Cyberplat» has decided to open the original source code of the CyberFT IT platform.
Identification in CyberFT Network
Each CyberFT Participant has their own ID (network address). Participant’s BIC is used as their address (address within the SWIFT system), unless that Participant has no BIC, in which case he is given a CyberFT address.
The Participant will connect to the CyberFT Network via processing. Processing with your own pool of Participant’s comprises a CyberFT Network segment. Processing is owned and controlled by the CyberFT Provider.
For electronic document exchange between the Participants of different segments of CyberFT Network, CyberFT Providers establishe a connection on the basis of bilateral electronic document exchange agreements.
For the purposes of security and legal validity of electronic document flow all CyberFT Participants and Providers first agree with the Global Rules of electronic document flow in CyberFT Network.
CyberFT terminal
Each participant uses a specialized software to interact with CyberFT Network – CyberFT Terminal that establishes a secure connection to the Provider for sending and receiving encrypted and signed data.
Electronic documents transmitted via CyberFT can be created in a variety of ways:
- Participant’s system, e.g. core banking / ERP / treasury / accounting system
- Terminal’s web-interface
- Integrated CyberFT software, e.g. a 1C electronic banking module
- Integrated bus of a participant
Scheme of integration of the Terminal with the Participant’s system during the electronic document exchange is depicted below:
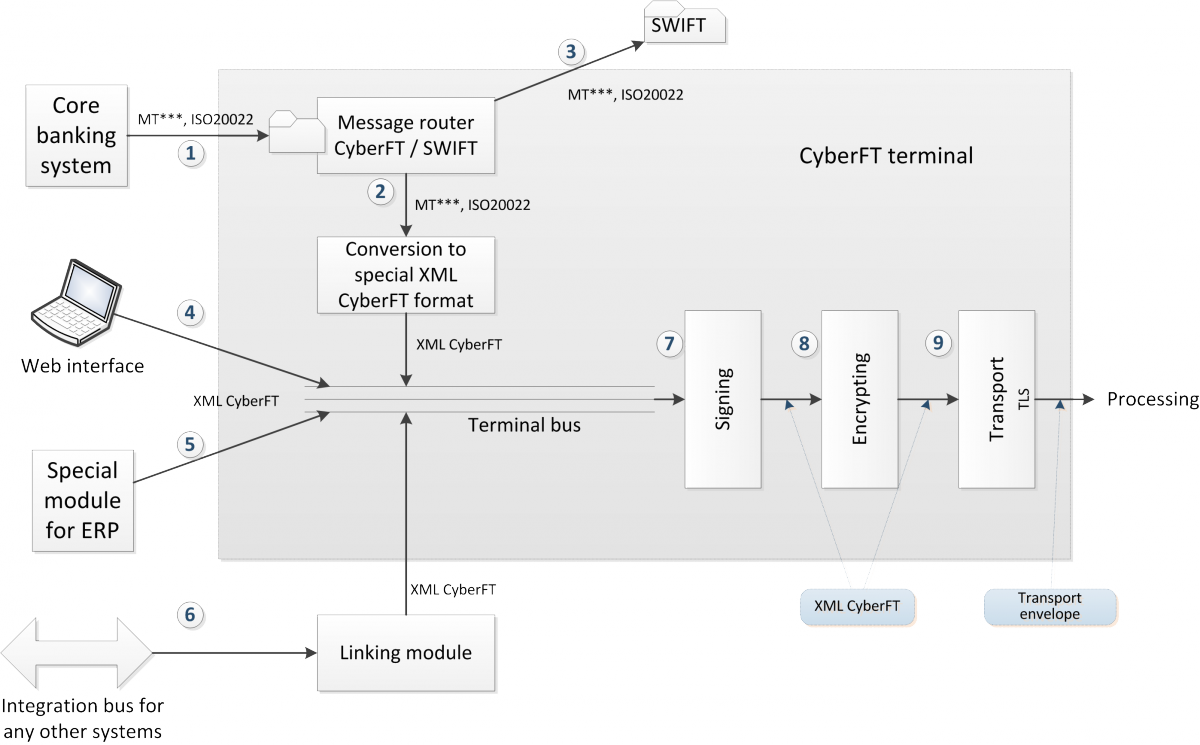
That said, the Terminal allows you to create / import documents from other systems in various formats, including SWIFT Fin and ISO20022, check the document for mistakes, sign, encrypt and send the document to the processing.
That said, the document can be signed both in the Terminal and in the participant’s system.
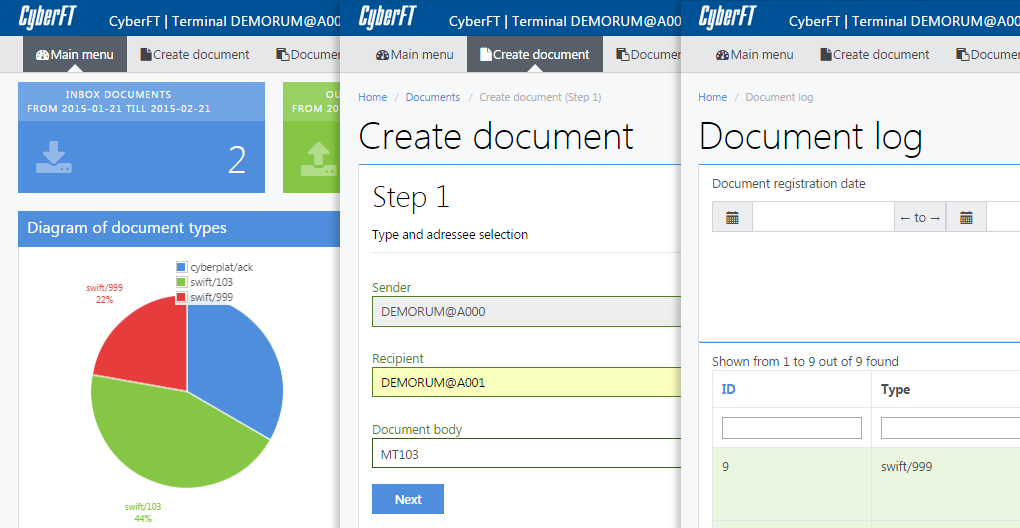
The Terminal boasts a convenient web-interface, which has little to no difference from the accustomed interface of electronic banking systems.
The Terminal has different user and signature access layers, which allows the customers to implement their local business rules and satisfy needs of the most companies.
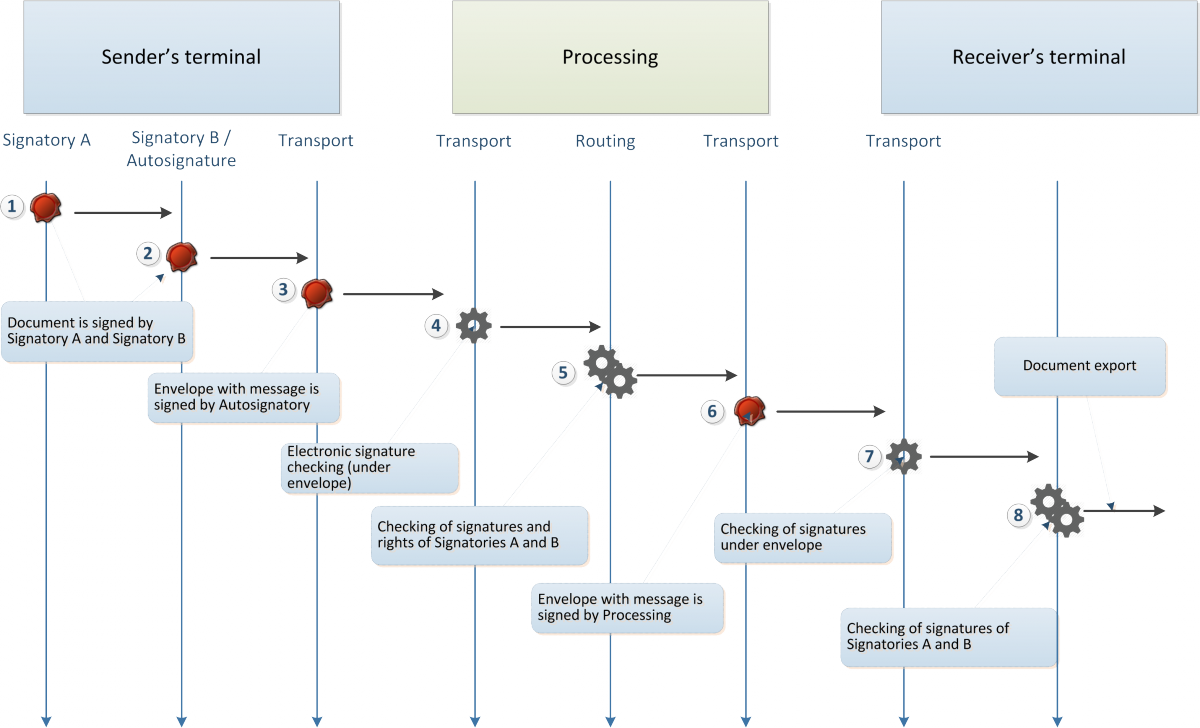
The document acceptance includes the opposite routine: processing e-signature check, document decryption, check of e-signatures below the document and forwarding of the document to the special catalogue / accounting system of the receiver, depending on the settings.
The scheme of document exchange via processing is depicted below:
SWIFT compatibility
Along with the Terminal comes a CyberFT customer application called Message Router, which allows you use CyberFT and SWIFT in parallel. This feature is mostly for banks that exchange data using both CyberFT and SWIFT. Scheme of Message Router operation is illustrated below:
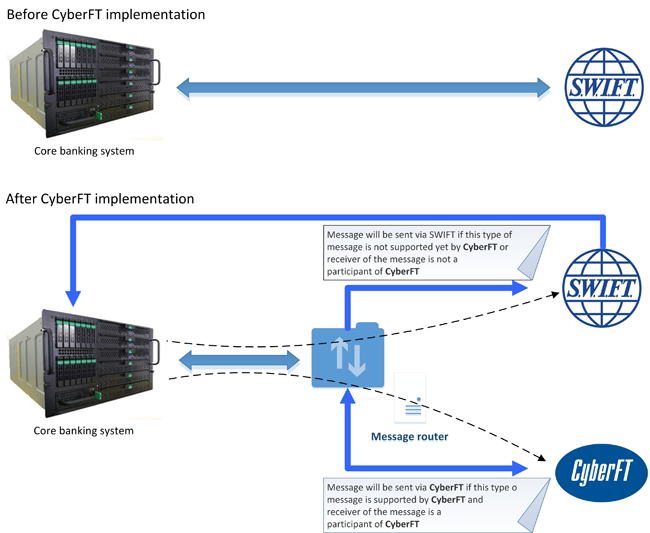
If a certain message type is supported by CyberFT and if the receiver of such a message is within CyberFT network, Message Router will forward that transaction to the CyberFT Provider who is within the country borders, which will come at a much lower price.
In case the required message type is not supported yet within CyberFT network, or the payment receiver is not connected to the CyberFT network, further transaction actions are done via SWIFT.
In case a new message type is developed or a new member is admitted, Message Router’s database is updated remotely.
