What is the purpose of the CyberFT Platform?
CyberFT Platform is a convenient and totally secure solution that allows its banks and their customers to:
 |
Optimize financial transaction costs |
 |
Guarantee integrity of information that contains trade secret |
 |
Operate in total conformity with local legislation |
 |
Be fully secured from external political threats |
 |
Set up direct connection between the client and the bank (host-to-host solution) without using of electronic banking system |
 |
Organize electronic documents workflow of legally valid documents between banks, corporate clients and public authorities |
 |
Establish information exchange between paying agents and banks duting the payments acceptance |
CyberFT – security element
Before the testimony of Edward Snowden regarding mass surveillance during the PACE on April 8, 2014 bank community was almost unaware of the threat posed by the data exchange containing bank secrets through SWIFT that is carried out through hubs and servers situated in the US, the Netherlands and Switzerland. However, from the stability viewpoint data of different hubs is supposed to be stored on the main server to restore data in case a system failure occurs.
All that in spite of the fact that security experts have been pointing out vulnerability of such a system for years, and they also emphasized that in all developed countries local (domestic) bank information is not allowed to cross borders of its country. Domestic interbank networks must be autonomous; otherwise state sovereignty might be jeopardized and might become dependable on hostile actions on behalf of the US or other forces.
Due to the fact that unlike many other systems operating on the global market all software was developed by Russian experts (license and patent independence), and all CyberFT Platform servers will be situated in the local territory of the platform Purchaser’s country, possibility of commercially vital data leak of electronic document flow significantly decreases.

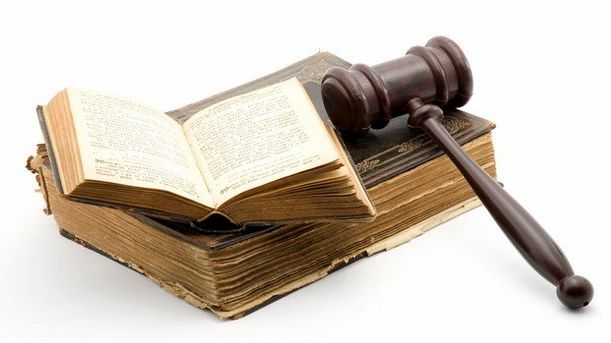
CyberFT Network is in full conformity with local legislation
In accordance with requirements of local legislation of the most countries domestic transactions shouldn’t be processed outside country’s borders. For instance, personal information of European countries (financial transaction nearly always contains personal information) cannot be processed outside the EU: The primary legal provision in the UK is Principle 8 of the Act which states that, "Personal data shall not be transferred to a country or territory outside the European Economic Area unless that country or territory ensures an adequate level of protection for the rights and freedoms of data subjects in relation to the processing of personal data."
Similar legislation is in force in Indonesia. According to the Government Regulation on implementation of electronic transaction system No. 82 dated 2012 public service operator must set up his own data processing center in Indonesia.
In early 2011 People’s Bank of China issued a Notification for bank financial institutions requiring security of financial information. Among other things, this Notification prohibits banks from storing, processing or analyzing any personal financial information collected in China beyond its borders.
CyberFT Platform is fully compliant with requirements of national payment legislation.
CyberFT Network ensures integrity of important commercial information
One of the key goals of CyberFT is to ensure security of information containing bank or trade secret. According to Zecurion in 2013 losses of both companies and banks from confidential information leaks exceeded USD 25 bn.
Vital commercial information processed by payment systems and transferred through communication channels is vulnerable to many threats, among which are:
- Security threat of interbank communications, since currently most of the SWIFT transactions (with minor exception) are processed through the servers situated in the territory of the US and Western Europe. Placement of servers in the US, the Netherlands and Switzerland compromises SWIFT customers from other countries, because at any point in time (e.g. due to the change in political situation) servers may be shut down, which in turn will cease data exchange not only with foreign banks-counterparties, but also domestic financial information exchange via the SWIFT system.
- Threat of theft directly from the system processing and effecting payments. The information may be both accessed at the request of the intelligence agency of a foreign country and intercepted by swindlers or other perpetrators at any section of communication line which can be as long as 20 000 km. Such information, typically related to the bank secret, may be exploited by thieves themselves or by persons that intercepted that information from thieves (as happened time and again in big recent international scandals).
- Threat of the leak of the previously stolen information. Big recent scandals (e.g. Snowden testimony or appearance of WikiLeaks) indicate that commercial information accessible to intelligence agencies can often become publicly available.
- Threat of handover of information to competitors. One of the examples of such a leak is a scandal that broke out in the US in the 90s, when because of the interception of talks by the National Security Agency, Airbus lost a USD 6 bn contract with a national airline company of Saudi Arabia. In the end, this contract was signed by McDonnell Douglas, subdivision of Boeing (main rival of Airbus).
- Threat of sale of stolen information. Today information is a valuable product – the more important it is the more valuable it is. That is why information containing trade and bank secret became a “honey pie” for cyber perpetrators.
As was stated above, protection against these threats is regulated by legislation of an array of countries that prohibit transfer of financial information across their borders or granting of access to such information in the territory of a foreign country.
Usage of CyberFT significantly reduces all risks of theft, loss or sale of vital information of banks and that of their customers. Since hardware will be located in the data center of the CyberFT Provider, the risk of commercial information theft from communication hub servers plummets, and since communication channels will be much shorter, the risk of theft of commercial information from communication lines will be much lower as well.
The message text sent by CyberFT participant (sender) to another participant (receiver) and that is not addressed to CyberFT Provider is accessible only to the message beneficiary, i.e. the customer.

